Takecertify collected actual Citrix 1Y0-440 questions and answers! The best way to pass the Citrix 1Y0-440 exam: Latest Update Citrix 1Y0-440 dumps, for the full 1Y0-440 dumps pdf, please click on (https://www.pass4itsure.com/1y0-440.html), Start your Citrix 1Y0-440 exam preparation today!
You can get the best tips to pass the Citrix 1Y0-440 exam:
By Google Drive | latest Citrix 1Y0-440 dumps pdf
[free, pdf] latest Citrix 1Y0-440 dumps pdf free download from Google Drive https://drive.google.com/file/d/1ebnsjXNGydhEmyS-C7tFxZyRxXCx55-O/view?usp=sharing
Citrix 1Y0-440 exam practice test questions 1-13 share online
QUESTION 1
Scenario: A Citrix Architect has set up NetScaler MPX devices in high availability mode with version 12.0.53.13 nc.
These are placed behind a Cisco ASA 5505 Firewall. The Cisco ASA Firewall is configured to block traffic using access
control lists. The network address translation (NAT) is also performed on the firewall.
The following requirements were captured by the architect during the discussion held as part of the NetScaler security
implementation project with the customer\\’s security team:
The NetScaler MPX device:
1.
should monitor the rate of traffic either on a specific virtual entity or on the device. It should be able to mitigate the
attacks from a hostile client sending a flood of requests. The NetScaler device should be able to stop the HTTP, TCP,
and DNS based requests.
2.
needs to protect backend servers from overloading.
3.
needs to queue all the incoming requests on the virtual server level instead of the service level.
4.
should provide protection against well-known Windows exploits, virus-infected personal computers, centrally managed
automated botnets, compromised webservers, known spammers/hackers, and phishing proxies.
5.
should provide flexibility to enforce the decided level of security check inspections for the requests originating from a
specific geolocation database.
6.
should block the traffic based on a pre-determined header length, URL length, and cookie length. The device should
ensure that characters such as a single straight quote (“); backslash (\); and semicolon (;) are either blocked,
transformed, or dropped while being sent to the backend server.
Which security feature should the architect configure to meet these requirements?
A. Global Server Load balancing with Dynamic RTT
B. Global Server Load Balancing with DNS views
C. Geolocation-based blocking using Application Firewall
D. geolocation-based blocking using Responder policies
Correct Answer: A
QUESTION 2
Scenario: A Citrix Architect has met with a team of Workspacelab members for a design discussion. They have captured
the following requirements for NetScaler design project:
1.
The authentication must be deployed for the users from the workspacelab.com and vendorlab.com domains.
2.
The workspacelab users connecting from the internal (workspacelab) network should be authenticated using LDAP.
3.
The workspacelab users connecting from the external network should be authenticated using LDAP and RADIUS.
4.
The vendorlab users should be authenticated using Active Directory Federation Service.
5.
The user credentials must NOT be shared between workspacelab and vendorlab.
6.
Single Sign-on must be performed between StoreFront and NetScaler Gateway.
7.
A domain drop down list must be provided if the used connects to the NetScaler gateway virtual server externally.
Which method must the architect utilize for user management between the two domains?
A. Create shadow accounts for the users of the Workspacelab domain in the Vendorlab domain.
B. Create a global catalog containing the objects of Vendorlab and Workspacelab domains.
C. Create shadow accounts for the Vendorlab domain in the Workspacelab domain.
D. Create a two-way trust between the Vendorlab and Workspacelab domains.
Correct Answer: B
QUESTION 3
Scenario: A Citrix Architect has implemented two high availability pairs of MPX 5500 and MPX 11500 devices
respectively with 12.0.53.13 nc version. The NetScaler devices are set up to handle NetScaler Gateway, Load
Balancing, Application Firewall, and Content Switching. The Workspacelab infrastructure is set up to be monitored with
NMAS version 12.0.53.13 nc by the Workspacelab administrators. The Workspacelab team wants to implement one
more pair of NetScaler MPX 7500 devices with version 12.0.53.13 nc.
The Citrix consulting team has assigned the task to implement these NetScaler devices in the infrastructure and set
them up to be monitored and managed by NMAS.
The following are the requirements that were discussed during the project initiation call:
1.
NMAS should be configured to get the infrastructure information under sections such as HDX Insight, WEB Insight, and
Security Insight.
2.
Configuration on the new MPX devices should be identical to MPX 11500 devices.
3.
Configuration changes after the deployment and initial setup should be optimized using NMAS.
4.
NMAS should be utilized to configure templates that can be utilized by the Workspacelab team in future deployment.
5.
As per the requirement from the Workspacelab team, NMAS should be store the audited data for only 15 days.
Which process should the architect utilize to ensure that the deployment of MPX 11500 devices are optimized and that it
is correct, before deploying the devices in production?
A. Under Stylebooks; Inbuilt and composite stylebook templates should be utilized prior to deployment.
B. Under Stylebooks; Public and composite stylebook templates should be utilized prior to deployment.
C. Under Configuration Management; Configuration Audit and Advice should be used prior to deployment.
D. Under Configuration jobs; Configuration Audit and Advice should be used prior to deployment.
Correct Answer: C
QUESTION 4
Scenario: A Citrix Architect needs to assess an existing NetScaler multi-site deployment. The deployment is using
Global Server Load Balancing (GSLB) configured in a parent-child configuration.
Click the Exhibit button to view the diagram of the current GSLB configuration and parent-child relationships, as well as
the status of the sites and the connectivity between them.
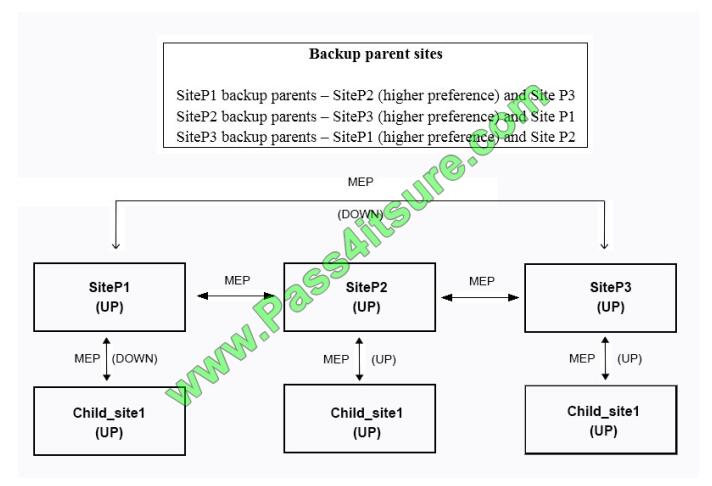
Based on the displayed configuration and status, Chil_site1_______ a connection from _______. (Choose the correct
option to complete the sentence.)
A. rejects; SiteP2 and SiteP3; remains a child site of SiteP1
B. rejects; SiteP3; remains a child site of SiteP1
C. accepts; SiteP3; becomes its child site
D. accepts; SiteP2; becomes its child site
E. does NOT receive; SiteP2 and SiteP3; remains a child site of SiteP1
F. rejects; SiteP2; remains a child site of SiteP1
Correct Answer: E
QUESTION 5
Scenario: A Citrix Architect needs to assess an existing NetScaler configuration. The customer recently found that
certain user groups were receiving access to an internal web server with an authorization configuration that does NOT
align with the designed security requirements.
Click the Exhibit button view the configured authorization settings for the web server.
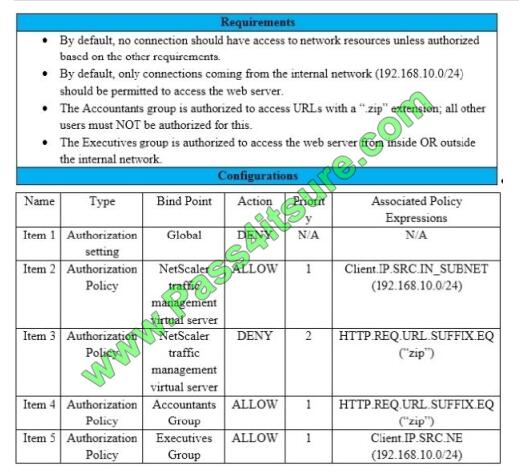
Which item should the architect change or remove to align the authorization configuration with the security requirements
of the organization?
A. Item 1
B. Item 3
C. Item 4
D. Item 5
E. Item 2
Correct Answer: E
QUESTION 6
Scenario: A Citrix Architect has deployed two MPX devices, 12.0.53.13 nc and MPX 11500 models, in high availability
(HA) pair for the Workspace labs team. The deployment method is two-arm and the devices are installed behind a
CISCO ASA 5585 Firewall. The architect enabled the following features on the NetScaler devices. Content Switching,
SSL Offloading, Load Balancing, NetScaler Gateway, Application Firewall in hybrid security and Appflow. All are
enabled to send monitoring information to NMAS 12.0.53.13 nc build. The architect is preparing to configure load
balancing for Microsoft Exchange 2016 server.
The following requirements were discussed during the implementation:
1.
All traffic needs to be segregated based on applications, and the fewest number of IP addresses should be utilized
during the configuration
2.
All traffic should be secured and any traffic coming into HTTP should be redirected to HTTPS.
3.
Single Sign-on should be created for Microsoft Outlook web access (OWA).
4.
NetScaler should recognize Uniform Resource Identifier (URl) and close the session to NetScaler when users hit the
Logoff button in Microsoft Outlook web access.
5.
Users should be able to authenticate using either user principal name (UPN) or sAMAccountName.
6.
The Layer 7 monitor should be configured to monitor the Microsoft Outlook web access servers and the monitor probes
must be sent on SSL
Which monitor will meet these requirements?
A. add lb monitor mon_rpc HTTP-ECV -send “GET /rpc/healthcheck.htm” recv 200 -LRTM DISABLED
B. add lb monitor mon_rpc HTTP-ECV -send “GET /rpc/healthcheck.htm” recv 200 -LRTM ENABLED
C. add lb monitor mon_rpc HTTP -send “GET /rpc/healthcheck.htm” recv 200 -LRTM DISABLED -secure YES
D. add lb monitor mon_rpc HTTP-ECV -send “GET/rpc/healthcheck.htm” recv 200 -LRTM DISABLED -secure YES
Correct Answer: A
QUESTION 7
Scenario: A Citrix Architect needs to assess an existing on-premises NetScaler deployment which includes Advanced
Endpoint Analysis scans. During a previous security audit, the team discovered that certain endpoint devices were able
to perform unauthorized actions despite NOT meeting pre-established criteria.
The issue was isolated to several endpoint analysis (EPA) scan settings.
Click the Exhibit button to view the endpoint security requirements and configured EPA policy settings.
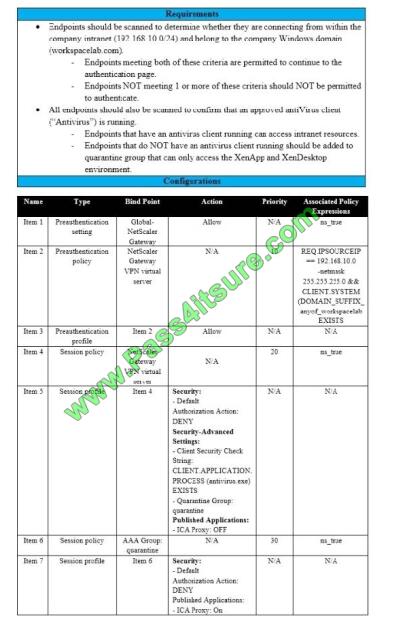
Which setting is preventing the security requirements of the organization from being met?
A. Item 6
B. Item 7
C. Item 1
D. Item 3
E. Item 5
F. Item 2
G. Item 4
Correct Answer: F
QUESTION 8
Scenario: A Citrix Architect needs to design a hybrid XenApp and XenDesktop environment which will include as well as
resource locations in an on-premises datacenter and Microsoft Azure.
Organizational details and requirements are as follows:
1.
Active XenApp and XenDesktop Service subscription
2.
No existing NetScaler deployment
3.
Minimization of additional costs
4.
All users should correct directly to the resource locations containing the servers which will host HDX sessions
Click the Exhibit button to view the conceptual environment architecture.
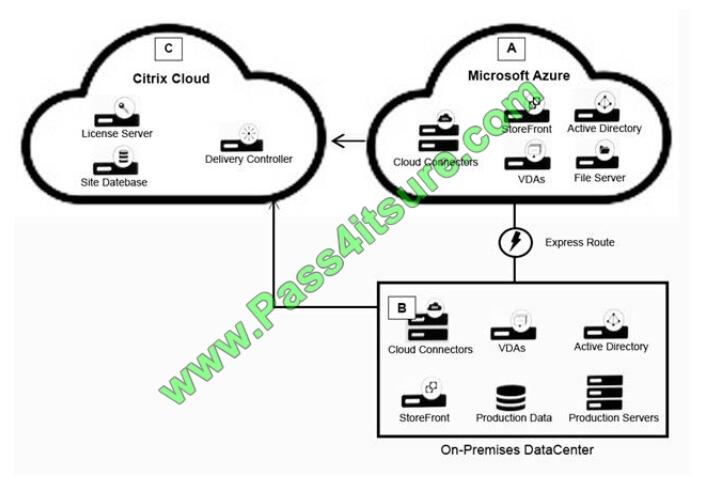
The architect should use___________ in Location A, and should use _______________ in Location B. (Choose the
correct option to complete the sentence.)
A. No NetScaler products; NetScaler ICA Proxy (cloud-licensed)
B. NetScaler Gateway as a Service; NetScaler ICA Proxy (cloud-licensed)
C. NetScaler Gateway as a Service; no NetScaler products
D. No NetScaler products; NetScaler Gateway appliance
E. NetScaler gateway as a Service; NetScaler ADC (BYO)
Correct Answer: C
QUESTION 9
Scenario: A Citrix Architect and a team of Workspacelab members have met for a design discussion about the
NetScaler Design Project. They captured the following requirements:
1.
Two pairs of NetScaler MPX appliances will be deployed in the DMZ network and the internal network.
2.
High availability will be accessible between the pair of NetScaler MPX appliances in the DMZ network.
3.
Multi-factor authentication must be configured for the NetScaler Gateway virtual server.
4.
The NetScaler Gateway virtual server is integrated with XenApp/XenDesktop environment.
5.
Load balancing must be deployed for the users from the workspacelab.com and vendorlab.com domains.
6.
The logon page must show the workspacelab logo.
7.
Certificate verification must be performed to identify and extract the username.
8.
The client certificate must have UserPrincipalName as a subject.
9.
All the managed workstations for the workspace users must have a client identifications certificate installed on it.
10.The workspacelab users connecting from a managed workstation with a client certificate on it should be
authenticated using LDAP. 11.The workspacelab users connecting from a workstation without a client certificate should
be
authenticated using LDAP and RADIUS.
12.The vendorlab users should be authenticated using Active Directory Federation Service.
13.The user credentials must NOT be shared between workspacelab and vendorlab.
14.Single Sign-on must be performed between StoreFront and NetScaler Gateway.
15.A domain drop down list must be provided if the user connects to the NetScaler Gateway virtual server externally.
16.The domain of the user connecting externally must be identified using the domain selected from the domain drop
down list.
On performing the deployment, the architect observes that users are always prompted with two-factor authentication
when trying to assess externally from an unmanaged workstation.
Click the exhibit button to view the configuration.
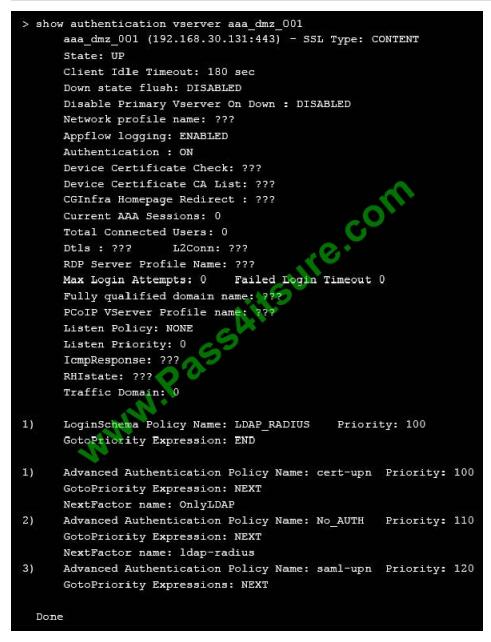
What should the architect do to correct this configuration?
A. Unbind LoginSchema Policy LDAP_RADIUS from the virtual server.
B. Bind the Portal theme as Domaindropdown.
C. Bind the LoginSchema Policy Domaindropdown to priority 90.
D. Bind the Default LoginSchema Policy as Domaindropdown.
Correct Answer: D
QUESTION 10
For which three reasons should a Citrix Architect perform a capabilities assessment when designing and deploying a
new NetScaler in an existing environment? (Choose three.)
A. Understand the skill set of the company.
B. Assess and identify potential risks for the design and build phase.
C. Establish and prioritize the key drivers behind a project.
D. Determine operating systems and application usage.
E. Identify other planned projects and initiatives that must be integrated with the design and build phase.
Correct Answer: BDE
QUESTION 11
A Citrix Architect has deployed NetScaler Management and Analytics System (NMAS) to monitor a high availability pair
of NetScaler VPX devices.
The architect needs to deploy automated configuration backup to meet the following requirements:
1.
The configuration backup file must be protected using a password.
2.
The configuration backup must be performed each day at 8:00 AM GMT.
3.
The configuration backup must also be performed if any changes are made in the ns.conf file.
4.
Once the transfer is successful, auto-delete the configuration file from the NMAS.
Which SNMP trap will trigger the configuration file backup?
A. netScalerConfigSave
B. sysTotSaveConfigs
C. netScalerConfigChange
D. sysconfigSave
Correct Answer: A
Reference: https://docs.citrix.com/en-us/netscaler-mas/12/instance-management/how-to-backup-and-restore-usingmas.html#configuring-instance-backup-settings
QUESTION 12
Scenario: Based on a discussion between a Citrix Architect and a team of Workspacelab members, the MPX Logical
layout for Workspacelab has been created across three (3) sites.
They captured the following requirements during the design discussion held for a NetScaler design project:
1.
All three (3) Workspacelab sites (DC, NDR, and DR) will have similar NetScaler configurations and design.
2.
Both external and internal NetScaler MPX appliances will have Global Server Load Balancing (GSLB) configured and
deployed in Active/Passive mode.
3.
GSLB should resolve both A and AAA DNS queries.
4.
In the GSLB deployment, the NDR site will act as backup for the DC site, whereas the DR site will act as backup for the
NDR site.
5.
When the external NetScaler replies to DNS traffic coming in through Cisco Firepower IPS, the replies should be sent
back through the same path.
6.
On the internal NetScaler, both the front-end VIP and backend SNIP will be part of the same subnet.
7.
The external NetScaler will act as default gateway for the backend servers.
8.
All three (3) sites, DC, NDR, and DR, will have two (2) links to the Internet from different service providers configured in
Active/Standby mode.
Which design decision must the architect make the design requirements above?
A. MAC-based Forwarding must be enabled on the External NetScaler Pair.
B. NSIP of the External NetScaler must be configured as the default gateway on the backend servers.
C. The Internal NetScaler must be deployed in Transparent mode.
D. The ADNS service must be configured with an IPv6 address.
Correct Answer: C
QUESTION 13
Scenario: A Citrix Architect needs to configure a full VPN session profile to meet the following requirements:
1.
Users should be able to send the traffic only for the allowed networks through the VPN tunnel.
2.
Only the DNS requests ending with the configured DNS suffix workspacelab.com must be sent to NetScaler Gateway.
3.
If the DNS query does NOT contain a domain name, then DNS requests must be sent to NetScaler gateway. Which
settings will meet these requirements?
A. Split Tunnel to OFF, Split DNS Both
B. Split Tunnel to ON, Split DNS Local
C. Split Tunnel to OFF, Split DNS Remote
D. Split Tunnel to ON, Split DNS Remote
Correct Answer: B
Pass4itsure Citrix dumps discount Code 2021 free share
Pass4itsure shares the latest Citrix exam discount code “Citrix”. Enter the discount code to get a 15% discount!
to sum up:
Are you looking for some tips to pass then I feel this is the best way to pass the 1Y0-440 exam: Get the full Citrix 1Y0-440 exam dumps to access the https://www.pass4itsure.com/1y0-440.html(Q&As Dumps). You can get the best tips here 1Y0-440 Understanding Citrix 1Y0-440 Sharing learning files: free Citrix 1Y0-440 online practice tests to help test your true strength! Citrix 1Y0-440 dumps pdf download online!