This is the latest updated free Microsoft MS-700 exam practice for 2025! Designed to help you understand the actual exam content.
Collaboratively compiled by multiple Microsoft 365 Certified professionals from Pass4itsure, it includes 471 of the latest exam questions and answers, covering all topic areas to help you focus and achieve success in the Microsoft 365 Certified: Teams Administrator Associate MS-700 exam.
This article is sponsored by Pass4itsure, sharing the 2025 Microsoft MS-700 exam practice questions and answers online!
| Exam Question Type | Quantity |
| Single & multiple choice | 272 |
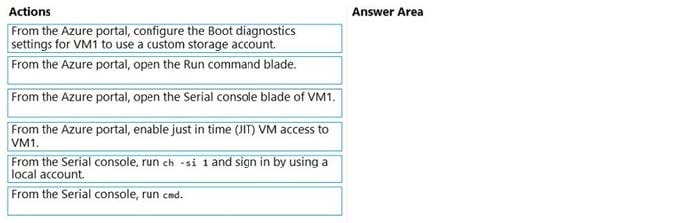
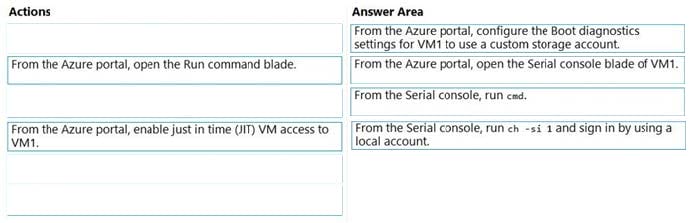
| Drag drop | 28 |
| Hotspot | 98 |
| Simulation Labs | 19 |
| Testlet | 3 |
MS-700 Online Practice Exam
To facilitate your repeated practice, I will print the latest exam questions and answers below as an MS-700 PDF for your convenient study anytime.
Q1:What should you do first?
You have a Microsoft Teams Phone deployment that uses Direct Routing.
You create a new Teams user named User1.
You need to enable User1 as an agent in a call queue.
A. Assign a dial plan to User1.
B. Assign a phone number to User1.
C. Enable hosted voicemail for User1.
D. Enable Enterprise Voice for User1.
Correct Answer: D
https://docs.microsoft.com/en-us/microsoftteams/plan-auto-attendant-call-queue
Q2:Which coexistence mode should you use?
You have a Microsoft Office 365 subscription.
You plan to upgrade from Microsoft Skype for Business to Microsoft Teams.
You use the following workloads in Skype for Business:
1.
Audio/video conferencing
2.
Dial-in conferencing
3.
Enterprise Voice
4.
Persistent Chat
5.
Chat
You need to ensure that users can evaluate Microsoft Teams while maintaining PSTN calling by using the Skype for Business client.
A. Islands
B. Skype for Business with Teams collaboration
C. Skype for Business only
D. Meetings First
Correct Answer: A
Q3:What should you configure?
Your company uses Microsoft Teams.
The company has 10 corporate images.
You want to provide the images to users as custom backgrounds for Teams meetings.
You need to make the backgrounds available to Teams users.
A. Meeting policies
B. Team templates
C. Meeting settings
D. Teams settings
Correct Answer: A
https://learn.microsoft.com/en-us/microsoftteams/custom-meeting-backgrounds
Q4:What should you do?
Your company has a Microsoft 365 subscription that uses Microsoft Office 365 E5 licenses and Azure Active Directory Premium Plan 1 licenses.
You have a team named Sales that contains all the users in the company\’s sales department.
You hire several new users in the sales department.
You discover that the new employees are never added to the team.
You need to ensure that when new sales department users are hired, they are added automatically to the team.
A. From the Microsoft Teams client, modify the settings of the Sales team.
B. From the Azure Active Directory admin center, modify the membership type of the Sales group.
C. From the Microsoft Teams admin center, modify the properties of the Sales team.
D. From the Microsoft 365 admin center, modify the settings of the Sales group.
Correct Answer: B
Reference: https://docs.microsoft.com/en-us/microsoftteams/dynamic-memberships https://docs.microsoft.com/en-us/azure/active-directory/users-groups-roles/groups-change-type
Q5:Which object must be associated with the auto attendant?
Your company has a Microsoft 365 subscription.
You need to create an auto attendant from the Microsoft Teams admin center.
A. Conferencing bridge
B. a shared mailbox
C. a Calling Plan
D. a resource account
Correct Answer: D
Reference: https://docs.microsoft.com/en-us/microsoftteams/create-a-phone-system-auto-attendant
Q6:Which three actions should you perform before you add the Contoso users to teams?
Each correct answer presents part of the solution.
Your company has a Microsoft 365 subscription.
You need to ensure that users from a partner company named Contoso, Ltd. can collaborate with your company\’s users in teams. The solution must ensure that the Contoso users can exchange chat messages in channels.
NOTE: Each correct selection is worth one point.
A. From the Services and add-ins settings in the Microsoft 365 admin center, set Let group members outside the organization access group content to On.
B. From the Guest access settings in the Microsoft Teams admin center, set Allow guest access in Microsoft Teams to On.
C. From the External collaboration settings in the Azure Active Directory admin center, add Contoso\’s domain to the list of target domains.
D. From the External access settings in the Microsoft Teams admin center, add Contoso\’s domain to the Allowed list of domains.
E. From the External collaboration settings in the Azure Active Directory admin center, set the option “Guest users permissions are limited” to No.
F. From the Services and add-ins settings in the Microsoft 365 admin center, set Let group owners add people outside the organization to groups to On.
Correct Answer: ABF
Q7:Which role should you assign to User1?
You have an Active Directory user named User1.
You need to ensure that User1 can view the following reports:
Microsoft Teams user activity report
Microsoft Teams device usage report
The solution must limit the ability of User1 to make changes to Microsoft 365 services.
A. Teams Service Administrator
B. Reports reader
C. Teams Communications Support Specialist
D. Message Center reader
Correct Answer: B
Reference: https://docs.microsoft.com/en-us/microsoftteams/teams-activity-reports
Q8:What should you review in the Microsoft Call Quality Dashboard?
You have a Microsoft 365 subscription that uses Microsoft Teams.
Users report poor call quality.
You need to identify whether Teams calls use TCP or UDP.
A. Endpoint Reports
B. Reliability Reports
C. Quality Drill Down Reports
D. Quality of Experience Reports
Correct Answer: D
To identify whether Teams calls are using TCP or UDP in the Microsoft Call Quality Dashboard, you should review the Quality of Experience Reports (option D). These reports provide detailed information on the quality of voice and video calls, including the network route used, packet loss, delay, and other metrics that can affect call quality. In these reports, you can identify whether calls are using UDP or TCP.
Q9:What should you configure?
You work as a Systems Administrator for your company. The company has recently purchased a subscription to Microsoft 365.
All users in your company have a Microsoft 365 E3 license.
You are in the process of configuring Microsoft Teams.
A company security policy states that users must not be able to add apps to Microsoft Teams.
You need to configure Microsoft Teams to meet the security requirement.
A. The global app permission policy.
B. The global Teams policy.
C. The Org-wide Teams settings.
D. The global app setup policy.
Correct Answer: A
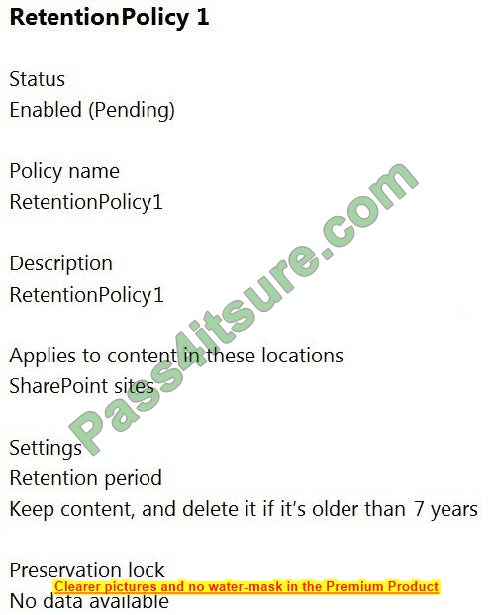
Q10:Which two locations should you apply the retention policy to?
(Choose two)
You work as a Systems Administrator for your company. The company has a subscription to Microsoft 365. All users in your company have a Microsoft 365 E3 license.
All users use Microsoft Teams for collaboration.
A company security policy has the following requirement:
All files used in personal chats or team collaborations must be retained for a minimum of one year.
You need to configure a retention policy to meet the security requirement.
A. OneDrive accounts
B. Exchange email
C. Teams chat
D. SharePoint sites
E. Teams channel messages
Correct Answer: AD
Q11:What should you use?
You have a Microsoft 365 subscription that uses Microsoft Teams.
You need to identify which teams were inactive during the past 90 days.
A. Teams advisor
B. The Teams user activity report
C. The Teams usage report
D. the Office 365 Groups activity report
Correct Answer: C
Reference: https://docs.microsoft.com/en-us/microsoftteams/teams-analytics-and-reports/teams-usage-report
Q12:What should you do?
You work as a Systems Administrator for your company. The company has a subscription to Microsoft 365. All users in your company have a Microsoft 365 E3 license.
All users use Microsoft Teams for collaboration.
Users in the company frequently invite external users to Microsoft Teams meetings.
Users report that when the guests join the meetings, they have to wait in the lobby until they are admitted by the meeting organizer.
You need to configure the system to ensure meeting participants join the meeting directly without waiting in the lobby.
A. Configure the Automatically admit users to Everyone setting in the global meeting policy.
B. Configure the Automatically admit users to Everyone in your organization setting in the global meeting policy.
C. Enable the Allow Meet now in channels setting in the global meeting policy.
D. Enable the Allow Meet now in private meetings setting in the global meeting policy.
Correct Answer: A
Q13:Does this meet the goal?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
Your company has a Microsoft 365 subscription that uses an Azure Active Directory (Azure AD) tenant named contoso.com.
You need to prevent guest users in the tenant from using cameras during Microsoft Teams meetings.
Solution: From Microsoft Teams admin center, you modify the Guest access settings.
A. Yes
B. No
Correct Answer: A
Guest access in Teams allows people outside you organization to access teams and channels. When you turn on Guest Access, you can turn on or off features guests users can or can’t use.
Reference: https://docs.microsoft.com/en-us/microsoftteams/set-up-guests
Q14: MS-700 SIMULATION
Please wait while the virtual machine loads. Once loaded, you may proceed to the lab section. This may take a few minutes, and the wait time will not be deducted from your overall test time.
When the Next button is available, click it to access the lab section. In this section, you will perform a set of tasks in a live environment.
While most functionality will be available to you as it would be in a live environment, some functionality
(e.g. copy and paste, ability to navigate to external websites) will not be possible by design.
Scoring is based on the outcome of performing the tasks stated in the lab. In other words it doesn’t matter how you accomplish the task, if you successfully perform it, you will earn credit for that task.
Labs are not timed separately, and this exam may have more than one lab that you must complete. You can use as much time as you would like to complete each lab.
But you should manage your time appropriately to ensure that you are able to complete the lab(s) and all other sections of the exam in the time provided.
Please not that once you submit your work by clicking the Next button within a lab, you will NOT be able to return to the lab.
You may now click next to proceed to the lab.
Username and password.
Use the following login credentials as needed:
To enter your username, place your cursor in the Sign in box and click on the username below.
To enter your password, place your cursor in the Enter password box and click on the password below.
Microsoft 365 Username:
[email protected] Microsoft 365 Password: XXXXXXXXXXXX
If the Microsoft 365 portal does not load successfully in the browser, press CTRL-K to reload the portal in a new browser tab.
The following information is for technical support purposes only:
Lab Instance: 26178313
Task 3
Adele Vance is a member of your company\’s technology adoption team.
You need to provide only Adele with the ability to turn on and off Teams preview features.
To complete this task, sign in to the Microsoft 365 portal.
Correct Answer: Check the answer in explanation.
Teams supports the ability to allow selected users to enable Public Preview features in the desktop and browser clients for an early view of functionality. You’ll need to create a new update policy in the Teams admin center and assign it to the people you want to access public preview.
Step 1: In Microsoft Teams admin center select Teams->Update policies
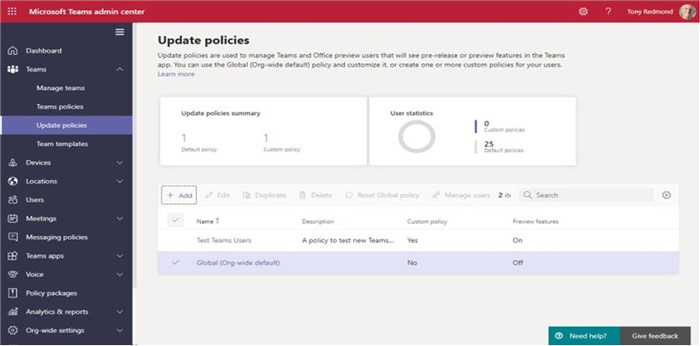
Step 2: Click Add
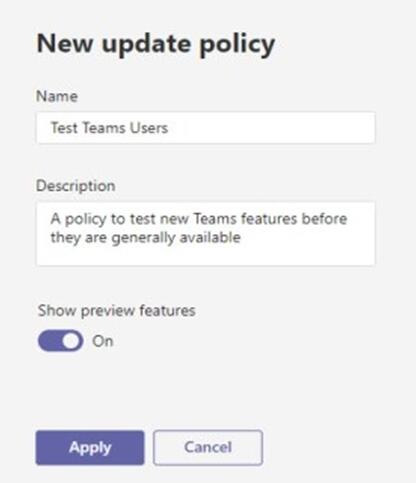
Step 3: Set Show preview features to On, and click Apply.
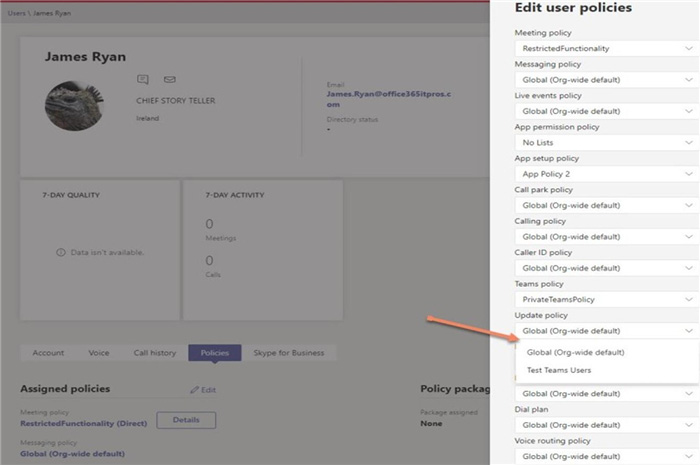
Step 4: In Microsoft Teams admin center select Users, and Adele.
Once the new update policy is saved, it can be assigned to user accounts.
You can do this by editing user accounts through the Teams admin center and editing the set of policies assigned to the account.
Step 5: In the Edit user policies window select Update policy and select the policy you defined.
Reference: https://office365itpros.com/2020/11/30/teams-preview-features/
Q15:What should you do in the Microsoft Teams admin center?
Your company has a Microsoft 365 subscription.
You need to customize meeting invitation emails to include the company logo.
A. From Teams settings, modify the Email integration settings.
B. From Meeting settings, modify the Email invitation settings.
C. From Meeting policies, create a new meeting policy and assign the policy.
D. From Meeting policies, modify the Global (Org-wide default) policy.
Correct Answer: B
TAC -> Meetings -> Meeting settings -> Email invitation section.
Reference: https://docs.microsoft.com/en-us/microsoftteams/meeting-settings-in-teams
…
We always prioritize sharing free MS-700 practical exam questions with all candidates, aiming to help you get the latest study materials as soon as possible. More learning methods are waiting for you to explore.
You can practice the latest 417 practical exam questions and answers using PDF or VCE tools at https://www.pass4itsure.com/ms-700.html. These resources will help you stay focused on your study goals and successfully earn the Microsoft 365 Certified: Teams Administrator Associate certification.
Advice for Beginners
The MS-700 exam is designed to validate your qualifications as a Microsoft Teams administrator. Therefore, the first step is to thoroughly study all the courses based on the official MS-700 study guide. You should understand exam updates, the latest skill assessments, the complete list of exam topics, and official learning resources.
Next, you should use the Pass4itsure MS-700 practical exam questions to identify knowledge gaps, simulate the test environment, and refine and strengthen your knowledge system.
The final step is to prepare for the exam.